Carlos_Castaneda_Books (detached pgp signature) Like any good book review ought to do, this one starts out with "here's the books I'm talking about" and "here's a way to verify you have the same ones I read". In this case the books are decent OCR scans and so who knows, perhaps are different in more substantial...
Month: May 2016
It's the economy, stupid!
So many public coins out there! Unfortunately, a lot of them have suffered from a problem of not considering the long term economics of their supply. Even bitcoin in fact, the original public coin, leaves something to be desired in this arena. Lets take a closer look. The issue is the money supply, and the...
Peter and the Wolf
http://frass.woodcoin.org/wp-content/uploads/2016/05/Peter-and-the-wolf.mp3 "Peter and the wolf" is right up there on the list of the greatest compositions of all time. This is one of my favorite performances of it, narrated by Ralph Richardson with the London Symphony Orchestra conducted by Malcolm Sargent. The piece is billed as being for "Children of All Ages", and it really...
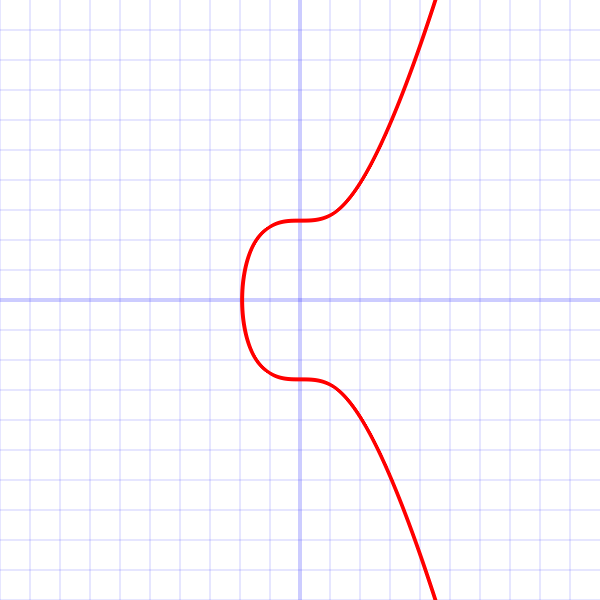
secp256k1 vs. p256
Round 1! (pun intended) A recent conversation brought this snippet in: ...prime256v1 is not a widely used curve for altcoins and is regarded as very unsafe to use... Every six months or so I return to this topic and repeat the research again, similar to the way I re-derive e.g. the quadratic equation and the chain...